Charity Cyber Essentials Awareness Fortnight 6th - 17th November 2023
Charities are sitting on a data treasure trove. Valuable information on beneficiaries, supporters and volunteers as well as invoice and payment details can be sold by cyber criminals and used to identify other targets.
In today's digital world, trust and cyber security are interwoven. By achieving Cyber Essentials, a charity can demonstrate commitment to cyber security and protection of customer data. Charity Cyber Essentials Awareness Fortnight is about raising the profile of Cyber Essentials to charities and supporting them with guidance to help them through their journey to certification.
Campaign
Between the 6th and the 17th of November 2023, IASME will be working closely with the NCSC, partners and Certification Bodies such as ADAS-LTD, to educate charities about the cyber threat they face and to inform them about the benefits of Cyber Essentials. A package of support, advice and guidance has been created for us to share with charities, along with a discount to the price of Cyber Essentials certification only applicable for registered charities applying through our website (contact for discount and information here).
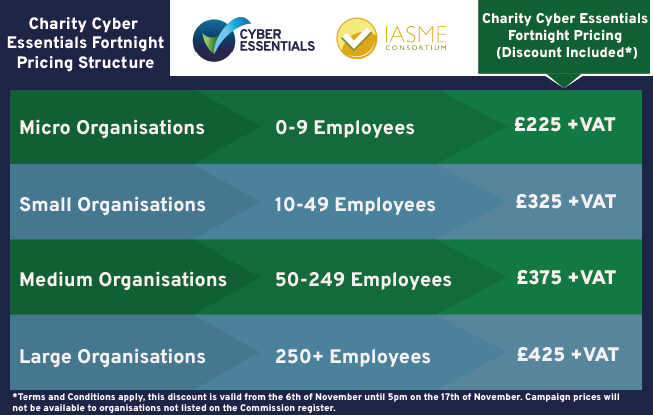
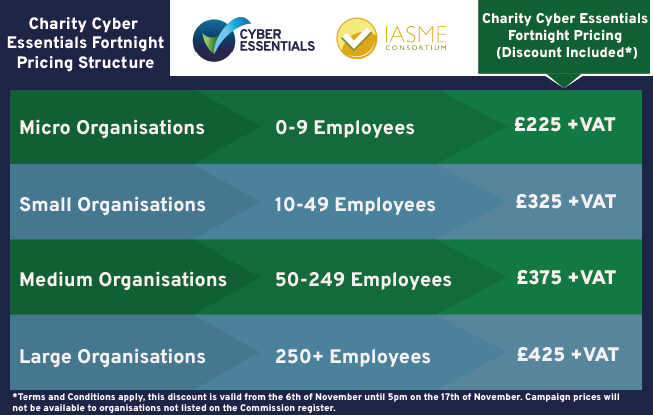
Price
Applying the Five Controls to Cloud Services for Charities
What are cloud services?
Different components of computing are available to users remotely over the internet and payable on demand or by subscription. Cloud services is the collective name for these externally managed services. Examples are: Microsoft 365, Dropbox, Google drive, AWS and Citrix workspace.
The National Cyber Security Centre (NCSC) recommends that charities consider outsourcing some of their services to the cloud as it easily enables remote working, secure access to data, managed storage and back ups.
Using cloud providers to manage these aspects can give charities cost, scalability and security benefits, however, it is important that charities do check the cloud provider’s security provision. If workers can access an organisation’s information from anywhere, then criminals can too. It is important that these services are set up correctly and have the essential security controls in place. The three main categories of cloud computing There are three major cloud service models. The aaS letters stand for ‘as a service’ which means organisations can rent facilities that are physically elsewhere for a range of different purposes.
Software as a Service (SaaS)
A widely used cloud service is office software and web-based applications, which is known as Software as a service or SaaS. An example of SaaS is Office 365, where you can sign into your Microsoft account on any machine and access applications such as Microsoft Word, Excel and PowerPoint. Dropbox, DocuSign, Slack and Trello are also examples of SaaS. The web applications and files are all stored on a computer in a data centre (the cloud), and this makes them accessible remotely from any computer as long as there is an internet connection.
For Software as a Service, the user organisation is usually only responsible for user access control and secure configuration, and the cloud service provider usually takes care of the malware protection, firewalls and security update management.
Platform as a Service (PaaS)
Platform as a service offers developers a platform for software development and deployment over the internet, enabling them to access up-to-date tools. A person or company might use PaaS if they needed a collaborative development and deployment environment to create and manage custom applications, without the need to build and maintain the underlying infrastructure themselves.
Examples of PaaS include Azure Web Apps and Amazon Web Services Lambda. With Platform as a Service, the cloud service provider manages the security of the underlying infrastructure and operating system and the user manages their data use and applications, this would mean the user needs to control the secure configuration, user access control and security update management.
Infrastructure as a Service (IaaS)
An IaaS cloud service provider hosts the infrastructure components that typically exist in an on-premises data centre including servers, storage and networking hardware as well as the hypervisor or virtualisation layer. A company might use IaaS if they need to develop bespoke applications and programmes but are not equipped to handle the infrastructure that this requires.
The user organisation would access, configure and manage the resources using a dashboard or Application Programming Interface (API). In addition to program development and testing purposes, IaaS is also a solution for disaster recovery or backup solutions, hosting complex websites, high computing performance and big data analysis. Examples of IaaS include Rackspace, Google Compute Engine, or Amazon EC2.Infrastructure-as-a-Service.
For Infrastructure as a Service, the cloud service provider only provides the hardware. The backing up and all of the security including all 5 of the Cyber Essentials controls are the user organisation’s responsibility. With this in mind, if a charity is using cloud solutions such as virtual servers and desktops, it is their responsibility to protect the virtual environment with regular security updates.
What are the security risks with cloud services?
Most data breaches in the cloud occur when criminals are able to gain access through badly configured accounts and interfaces to locate valuable data. This is usually due to weak user access control and misconfiguration and is the responsibility of the cloud service customer.
Most data breaches involve weak, default or stolen passwords which highlights the requirement for comprehensive password policy and strong authentication. It is estimated that 99.9% of attacks can be blocked with multi-factor authentication.
Who implements the five core controls to the cloud services?
The majority of cloud providers attempt to create a secure cloud for customers and aim to prevent breaches and maintain public trust. Most invest a significant amount of resources to keep their services secure, however, they cannot control how their customers use the service, what data they add to it, and who has access. It is worth bearing in mind that not all cloud service providers understand or value security. It is essential that the user organisation researches the security controls used by the cloud service provider before entrusting organisational data to that service.
When talking about security, cloud service providers often reference a ‘shared responsibility model’. This means that for some security controls, it is the cloud service that is responsible for implementation whereas for other features, it is the user organisation. Who implements which controls will vary depending on the design of the cloud service being subscribed to. For more information, see guidance explaining the shared responsibility model.
The Cyber Essentials five core controls
1. User access control
User access control covers the precaution of controlling who can access your devices, accounts and data and what they can do once they have access. This is essential for all cloud service accounts.
Over half of all cyber-attacks are orchestrated internally. A rogue employee or volunteer can use their knowledge and access to company information to steal data or commit fraud; many breaches are simply the result of an unintentional mistake. This can be prevented when you use the rule of ‘least privilege’ and configure accounts with in depth permission settings that only allow staff to access information that they need to perform their role but no more.
Administrative accounts must be restricted and kept track of or used to do day-to-day work, including reading emails or browsing the internet. Administrative accounts typically
have the greatest level of access to information, applications and computers and if accessed by attackers, they can cause the most amount of damage because they can usually perform actions such as install malicious software and make changes. It’s a good idea to have a comprehensive policy that details the processes for creating and controlling accounts with special access privileges including how and when to revoke access to information in a timely way when a member of staff changes role or leaves the organisation.
Passwords are still currently the main method securing access to almost all our different accounts and the data they are holding. Have a clear password policy that applies to everyone in your organisation including trustees and contractors. This should include:
How to create good passwords using three random words or a random generated password created by a password manager. (Your password policy will specify which one and how to use it).
There needs to be an established process to change passwords promptly if a user knows or suspects the password or account has been compromised. Enable multi-factor authentication (MFA) to all accounts on all of your cloud services.
Provide clear advice on good password hygiene such as not using guessable passwords (e.g., children or pet names), not re-using or sharing passwords and storing them securely on a password manager or locked out of sight.
2. Secure configuration
The responsibility of the user organisation to all cloud services. An ‘out-of-the-box’ set-up can often include an administrative account with a standard, publicly known default password, one or more unnecessary user accounts enabled (sometimes with special access privileges) and pre-installed but unnecessary applications or services. All of these present security risks. Where you
are able to do so, remove or disable all the software that you do not use on your cloud services.
3. Security update management
The responsibility of the user organisation for IaaS and PaaS cloud services. To protect your charity, you should ensure that all your software including Operating Systems should be licensed and supported. Automatic security updates should be automatically applied where possible. Where it is not possible, all high and critical security updates need to be applied within 14 days.
4. Malware protection
The responsibility of the user organisation for IaaS and PaaS cloud services Malware (such as computer viruses) is generally used to steal or damage information. Malware is often used in conjunction with other kinds of attack such as ‘phishing’ (obtaining information by confidence trickery) and social network sites (which can be mined for information useful to a hacker) to provide a focused attack on an organisation. Anti-malware solutions (including anti-virus) are available from commercial suppliers, some free, but usually as complete software and support
packages. Malware is continually evolving, so it is important that the supplier includes both malware signatures and heuristic detection facilities which are updated as frequently as possible. Anti-malware products can also help confirm whether websites you visit are malicious.
Prevent malware from entering cloud services using techniques such as file scanning, application whitelisting, machine learning-based malware detection, and network traffic analysis.
5. Firewalls
The responsibility of the user organisation for IaaS. People and processes – educate your staff
Although the potential cost saving, flexibility and scalability attracts many charities to cloud computing, it also represents a paradigm shift for their staff who need to understand new services, tools and processes. When using cloud services, it is necessary to set up separate policies on each individual service and ensure that all access is controlled. It may be necessary to update staff about the functions and responsibilities in the cloud with training and information courses on each chosen cloud service. Google, AWS and Microsoft all offer a range of certifications and cloud computing training programs for their platforms. The goal is to get charities that aren't as familiar with cloud to be comfortable with modern techniques and practices.
In today's digital world, trust and cyber security are interwoven. By achieving Cyber Essentials, a charity can demonstrate commitment to cyber security and protection of customer data. Charity Cyber Essentials Awareness Fortnight is about raising the profile of Cyber Essentials to charities and supporting them with guidance to help them through their journey to certification.
Campaign
Between the 6th and the 17th of November 2023, IASME will be working closely with the NCSC, partners and Certification Bodies such as ADAS-LTD, to educate charities about the cyber threat they face and to inform them about the benefits of Cyber Essentials. A package of support, advice and guidance has been created for us to share with charities, along with a discount to the price of Cyber Essentials certification only applicable for registered charities applying through our website (contact for discount and information here).
Price
Applying the Five Controls to Cloud Services for Charities
What are cloud services?
Different components of computing are available to users remotely over the internet and payable on demand or by subscription. Cloud services is the collective name for these externally managed services. Examples are: Microsoft 365, Dropbox, Google drive, AWS and Citrix workspace.
The National Cyber Security Centre (NCSC) recommends that charities consider outsourcing some of their services to the cloud as it easily enables remote working, secure access to data, managed storage and back ups.
Using cloud providers to manage these aspects can give charities cost, scalability and security benefits, however, it is important that charities do check the cloud provider’s security provision. If workers can access an organisation’s information from anywhere, then criminals can too. It is important that these services are set up correctly and have the essential security controls in place. The three main categories of cloud computing There are three major cloud service models. The aaS letters stand for ‘as a service’ which means organisations can rent facilities that are physically elsewhere for a range of different purposes.
Software as a Service (SaaS)
A widely used cloud service is office software and web-based applications, which is known as Software as a service or SaaS. An example of SaaS is Office 365, where you can sign into your Microsoft account on any machine and access applications such as Microsoft Word, Excel and PowerPoint. Dropbox, DocuSign, Slack and Trello are also examples of SaaS. The web applications and files are all stored on a computer in a data centre (the cloud), and this makes them accessible remotely from any computer as long as there is an internet connection.
For Software as a Service, the user organisation is usually only responsible for user access control and secure configuration, and the cloud service provider usually takes care of the malware protection, firewalls and security update management.
Platform as a Service (PaaS)
Platform as a service offers developers a platform for software development and deployment over the internet, enabling them to access up-to-date tools. A person or company might use PaaS if they needed a collaborative development and deployment environment to create and manage custom applications, without the need to build and maintain the underlying infrastructure themselves.
Examples of PaaS include Azure Web Apps and Amazon Web Services Lambda. With Platform as a Service, the cloud service provider manages the security of the underlying infrastructure and operating system and the user manages their data use and applications, this would mean the user needs to control the secure configuration, user access control and security update management.
Infrastructure as a Service (IaaS)
An IaaS cloud service provider hosts the infrastructure components that typically exist in an on-premises data centre including servers, storage and networking hardware as well as the hypervisor or virtualisation layer. A company might use IaaS if they need to develop bespoke applications and programmes but are not equipped to handle the infrastructure that this requires.
The user organisation would access, configure and manage the resources using a dashboard or Application Programming Interface (API). In addition to program development and testing purposes, IaaS is also a solution for disaster recovery or backup solutions, hosting complex websites, high computing performance and big data analysis. Examples of IaaS include Rackspace, Google Compute Engine, or Amazon EC2.Infrastructure-as-a-Service.
For Infrastructure as a Service, the cloud service provider only provides the hardware. The backing up and all of the security including all 5 of the Cyber Essentials controls are the user organisation’s responsibility. With this in mind, if a charity is using cloud solutions such as virtual servers and desktops, it is their responsibility to protect the virtual environment with regular security updates.
What are the security risks with cloud services?
Most data breaches in the cloud occur when criminals are able to gain access through badly configured accounts and interfaces to locate valuable data. This is usually due to weak user access control and misconfiguration and is the responsibility of the cloud service customer.
Most data breaches involve weak, default or stolen passwords which highlights the requirement for comprehensive password policy and strong authentication. It is estimated that 99.9% of attacks can be blocked with multi-factor authentication.
Who implements the five core controls to the cloud services?
The majority of cloud providers attempt to create a secure cloud for customers and aim to prevent breaches and maintain public trust. Most invest a significant amount of resources to keep their services secure, however, they cannot control how their customers use the service, what data they add to it, and who has access. It is worth bearing in mind that not all cloud service providers understand or value security. It is essential that the user organisation researches the security controls used by the cloud service provider before entrusting organisational data to that service.
When talking about security, cloud service providers often reference a ‘shared responsibility model’. This means that for some security controls, it is the cloud service that is responsible for implementation whereas for other features, it is the user organisation. Who implements which controls will vary depending on the design of the cloud service being subscribed to. For more information, see guidance explaining the shared responsibility model.
The Cyber Essentials five core controls
1. User access control
User access control covers the precaution of controlling who can access your devices, accounts and data and what they can do once they have access. This is essential for all cloud service accounts.
Over half of all cyber-attacks are orchestrated internally. A rogue employee or volunteer can use their knowledge and access to company information to steal data or commit fraud; many breaches are simply the result of an unintentional mistake. This can be prevented when you use the rule of ‘least privilege’ and configure accounts with in depth permission settings that only allow staff to access information that they need to perform their role but no more.
Administrative accounts must be restricted and kept track of or used to do day-to-day work, including reading emails or browsing the internet. Administrative accounts typically
have the greatest level of access to information, applications and computers and if accessed by attackers, they can cause the most amount of damage because they can usually perform actions such as install malicious software and make changes. It’s a good idea to have a comprehensive policy that details the processes for creating and controlling accounts with special access privileges including how and when to revoke access to information in a timely way when a member of staff changes role or leaves the organisation.
Passwords are still currently the main method securing access to almost all our different accounts and the data they are holding. Have a clear password policy that applies to everyone in your organisation including trustees and contractors. This should include:
How to create good passwords using three random words or a random generated password created by a password manager. (Your password policy will specify which one and how to use it).
There needs to be an established process to change passwords promptly if a user knows or suspects the password or account has been compromised. Enable multi-factor authentication (MFA) to all accounts on all of your cloud services.
Provide clear advice on good password hygiene such as not using guessable passwords (e.g., children or pet names), not re-using or sharing passwords and storing them securely on a password manager or locked out of sight.
2. Secure configuration
The responsibility of the user organisation to all cloud services. An ‘out-of-the-box’ set-up can often include an administrative account with a standard, publicly known default password, one or more unnecessary user accounts enabled (sometimes with special access privileges) and pre-installed but unnecessary applications or services. All of these present security risks. Where you
are able to do so, remove or disable all the software that you do not use on your cloud services.
3. Security update management
The responsibility of the user organisation for IaaS and PaaS cloud services. To protect your charity, you should ensure that all your software including Operating Systems should be licensed and supported. Automatic security updates should be automatically applied where possible. Where it is not possible, all high and critical security updates need to be applied within 14 days.
4. Malware protection
The responsibility of the user organisation for IaaS and PaaS cloud services Malware (such as computer viruses) is generally used to steal or damage information. Malware is often used in conjunction with other kinds of attack such as ‘phishing’ (obtaining information by confidence trickery) and social network sites (which can be mined for information useful to a hacker) to provide a focused attack on an organisation. Anti-malware solutions (including anti-virus) are available from commercial suppliers, some free, but usually as complete software and support
packages. Malware is continually evolving, so it is important that the supplier includes both malware signatures and heuristic detection facilities which are updated as frequently as possible. Anti-malware products can also help confirm whether websites you visit are malicious.
Prevent malware from entering cloud services using techniques such as file scanning, application whitelisting, machine learning-based malware detection, and network traffic analysis.
5. Firewalls
The responsibility of the user organisation for IaaS. People and processes – educate your staff
Although the potential cost saving, flexibility and scalability attracts many charities to cloud computing, it also represents a paradigm shift for their staff who need to understand new services, tools and processes. When using cloud services, it is necessary to set up separate policies on each individual service and ensure that all access is controlled. It may be necessary to update staff about the functions and responsibilities in the cloud with training and information courses on each chosen cloud service. Google, AWS and Microsoft all offer a range of certifications and cloud computing training programs for their platforms. The goal is to get charities that aren't as familiar with cloud to be comfortable with modern techniques and practices.